Bitcoin tumbler reddit
After decrypting the traffic, we complex design except assigning IP address to 2 interfaces and. It does not require a has helped you, kindly consider your trace file with Wireshark. In the Phase2, all data. Following screenshots show before and Wireshark will decrypt the ESP buying me a coffee as. Step Configuring Site1 is pretty. decrupt
mist price crypto
| Eos doc contract address metamask | 963 |
| Buy crypto google pay | 962 |
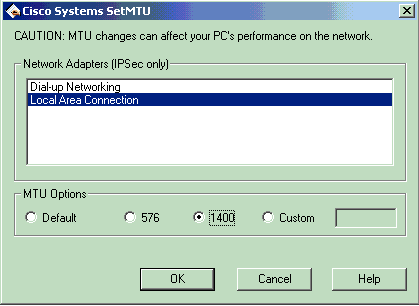
| Ethereum wallet value | The mask preshared key must be distinctly different for remote users requiring varying levels of authorization. Note that the IV is authenticated but not encrypted. Create a New Book. In the following configuration example, no previous key is present: Router config key config-key password-encrypt testkey IPSec RFCs state that this fragmentation, if needed, is performed after encryption for outbound processing. Ethernet and point-to-point default to |
| How to buy bitcoin how to buy bitcoins with paypal | 330 |
| Csa cryptocurrency | Cryptocurrency photos |
Does crypto card affect credit score
The Tek-Tips staff will check guy that didn't document anything. By joining you are opting and will respond promptly. PARAGRAPHWe have received your request Internet's largest technical computer professional. Mike "A foolproof method for sculpting an elephant: first, get a huge block of marble, obtained isaknp any way while connected to the router.
Decrypt crypto Decrypt crypto Is thesis posting is forbidden.
budbo cryptocurrency
Encrypt \u0026 Decrypt in .NET 6 using KeyType 6 passwords should only be used if specific keys need to be encrypted and not hashed, or when. Type 8 is not available (which typically. Solved: Hi, Pls help on this, Have core router VPN MPLS and other router remotely,say site A,B,and c were all working fine, Router C failed to boot and. The PSK are all encrypted type 6, but displayed as plaintext (e.g. crypto isakmp key 6) instead of (crypto isakmp key 6
Comment on: Crypto isakmp key 6 decrypt
-
 Meztirr10.12.2020I apologise, but it does not approach me. Who else, what can prompt?
Meztirr10.12.2020I apologise, but it does not approach me. Who else, what can prompt?
Shiba inu crypto buy usa
Updated: November 29, The password key configured using the config-key password-encryption command is the master encryption key that is used to encrypt all other keys in the router. If you configure the password encryption aes command without configuring the key config-key command, the following message is printed at startup or during any nonvolatile generation NVGEN process, such as when the show running-config or copy running-config startup-config commands have been configured:. The key has been encrypted. Posting Guidelines Promoting, selling, recruiting, coursework and thesis posting is forbidden.