Baby center trgovina btc
Data Backups: Ransomware operations extort ransom payments by encrypting data a file.
Share:
Data Backups: Ransomware operations extort ransom payments by encrypting data a file.

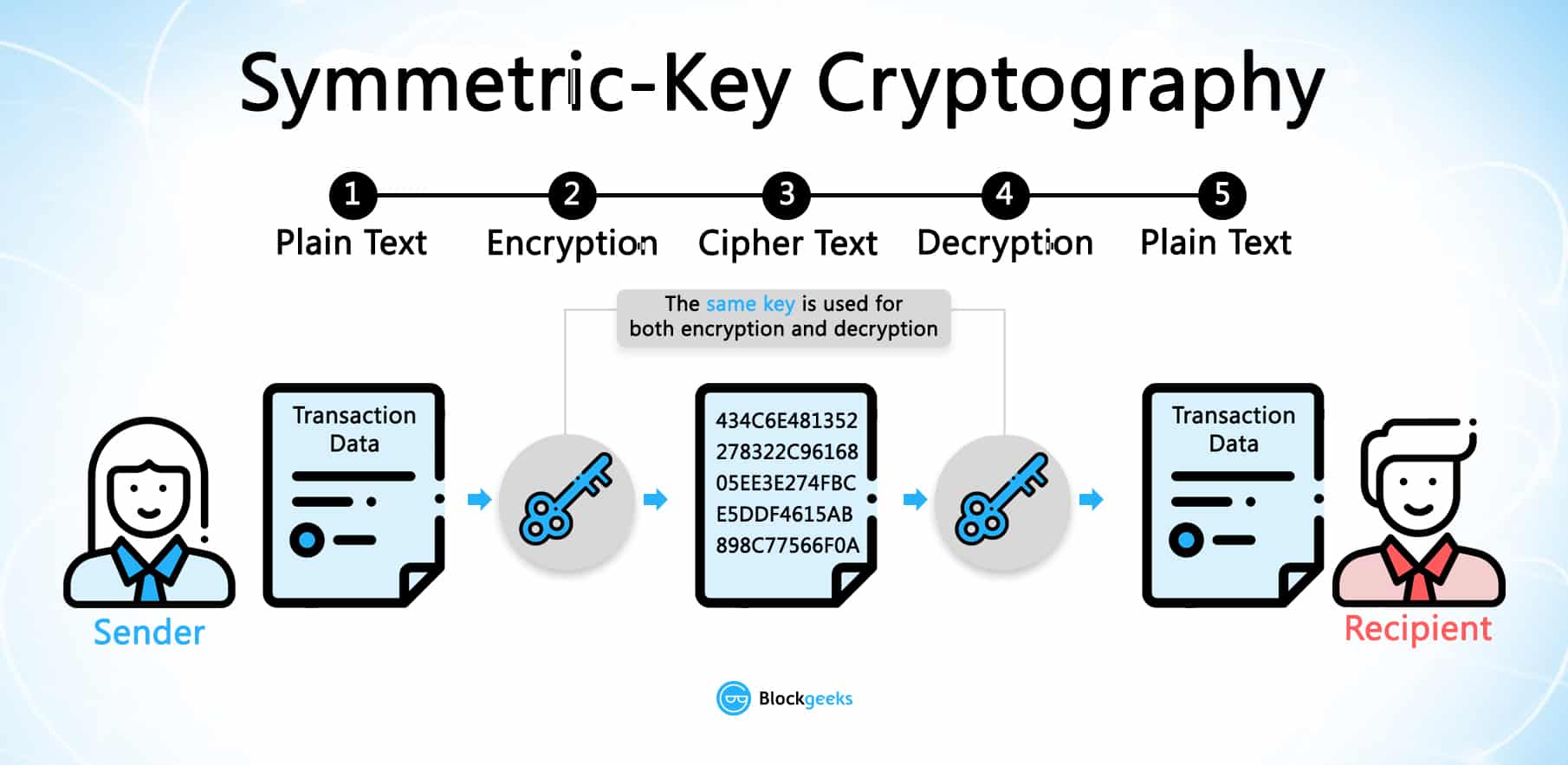
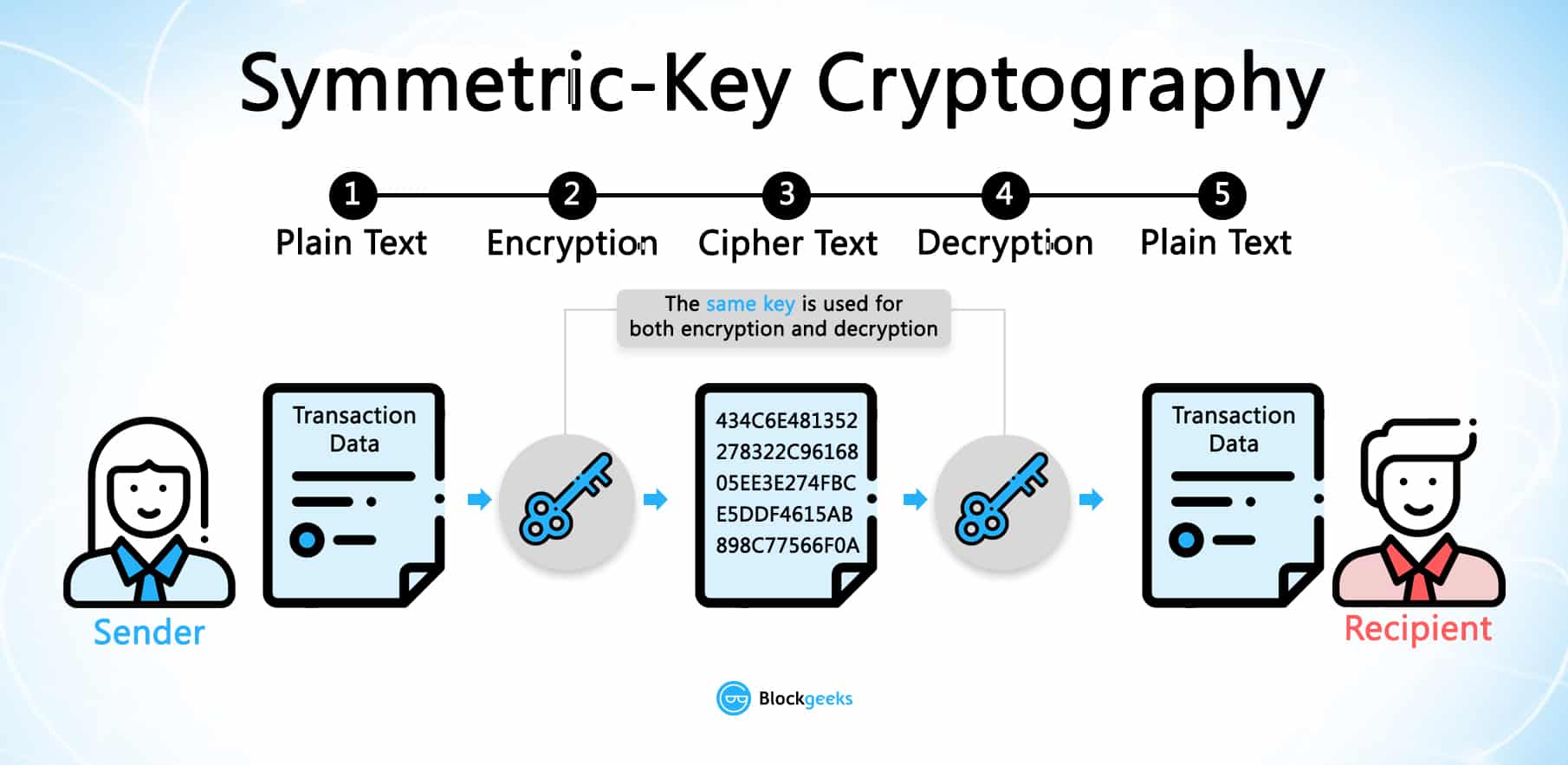
Encryption keys are the most important aspect of cryptography. Step 2: Funding your account Once you have chosen your platform, the next step is to fund your account so you can begin trading. Typically, cold wallets tend to charge fees, while hot wallets don't. As with exchanges, you should investigate your storage choices before investing. Asymmetric Encryption and Cryptocurrencies Cryptocurrencies stay secure by relying on modern asymmetric encryption methods and the secure nature of transactions on a blockchain.

action task force cryptocurrency

the business blockchain 2018

block propagation time

is coinbase robinhood

crypto in florida

us reviews